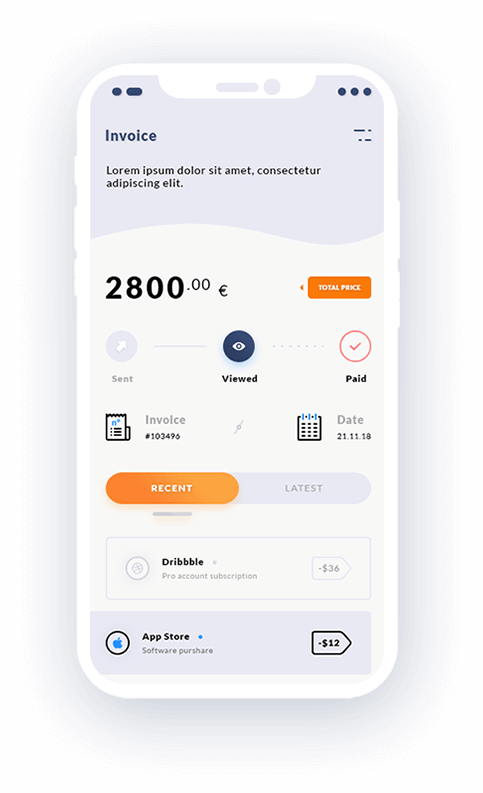
A bunch of experienced and honest developers. Their acumen of developing a software product is unbeatable and is worth hiring. It was difficult to match their energy at times. I truly appreciate their capability to plan future features of the app in an intelligent way. Thanks guys.